Prerequisites:
See Using JumpCloud’s LDAP-as-a-Service to obtain the JumpCloud specific settings required below.
This process was qualified on 12/01/2016 with iDRAC8 v2.40.40.40.
The following configuration information will allow for LDAP authentication with the Integrated Dell Remote Access Controller (iDRAC).
LDAP Settings:
Generic LDAP Enabled: Yes
Use Distinguished Name to Search Group Membership: Yes
LDAP Server Address: ldap.jumpcloud.com
LDAP Server Port: 636 (or 389 not supported)
Bind DN: uid=LDAP_BINDING_USER,ou=Users,o=YOUR_ORG_ID,dc=jumpcloud,dc=com
Bind Password: LDAP_BINDING_USER_PASSWORD
Base DN to Search: ou=Users,o=YOUR_ORG_ID,dc=jumpcloud,dc=com
Attribute of User Login: uid
To leverage LDAP Groups, see Creating LDAP Groups. NOTE: Any member of this group should also be set as an LDAP binding user in their User Details. This is necessary because after the iDRAC performs the initial authentication, it attempts to use the unique uid of the authenticated user to search LDAP for group membership and authorization to resources.
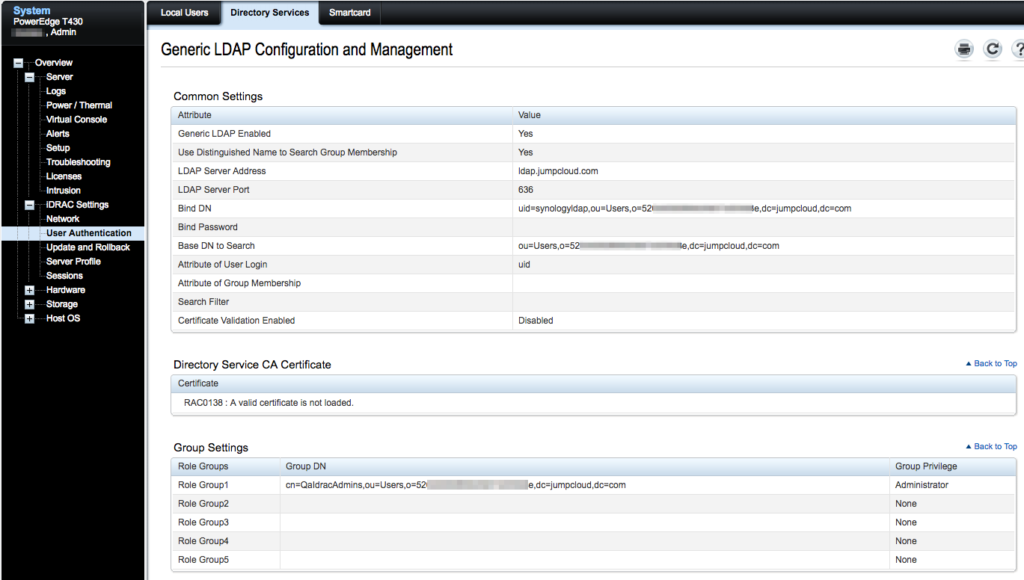
To add group privilege, define a Group DN under one of the Role GroupN settings.
Group DN: cn=GROUP_NAME,ou=Users,o=YOUR_ORG_ID,dc=jumpcloud,dc=com